Conflict between IT and OT hindering safety of industrial systems, SANS survey

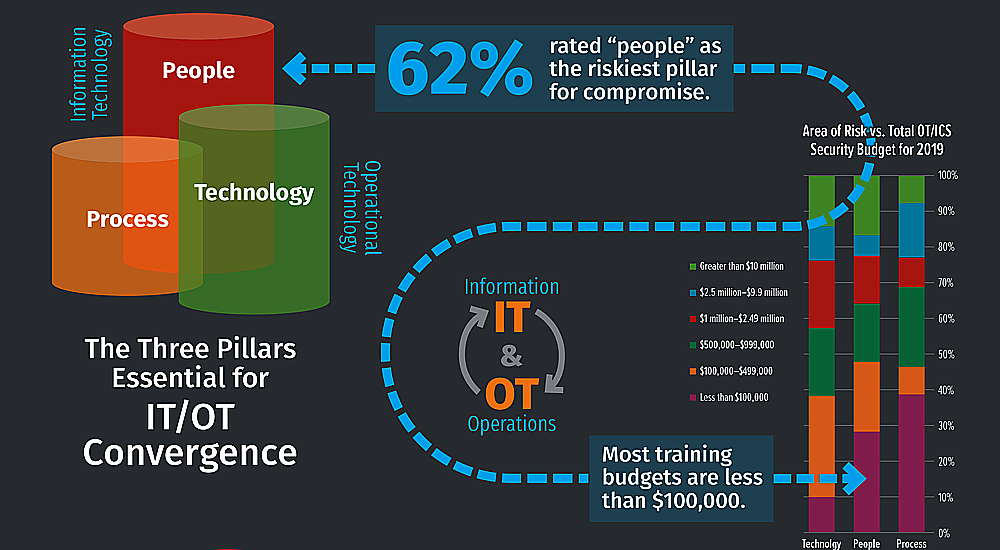
People remain the greatest threat to industrial control systems, ICS and associated networks, according to a new SANS survey focused on better understanding cybersecurity risks to operational technology, OT systems. More than half of respondents also see the cyber risks to their safe and reliable operations as high or higher than in past years.
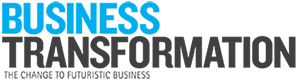
Three hundred and forty-eight security professionals worldwide, representing IT, OT and hybrid IT-OT domains provided their thoughts in the SANS 2019 State of OT, ICS Cybersecurity Survey. 62% of those surveyed believe people are the greatest risk to cyber security compromise, trailed by technology 22% and processes and procedures 14%.
Survey takers told SANS that identifying connected assets and gaining visibility into device, network and control system integrity remains an issue: 45.5% consider it a leading focus for their organisations. That aligns with traditional IT security concerns in which identifying and tracking assets and networks remains a challenge. Not surprisingly, mobile devices including those used remotely to augment and replace ICS workstations, and wireless communications solutions are contributors to overall risks and threat exposure.
“Do not underestimate that your biggest challenge with integrating will be changing the mindset of both IT and OT to think like each other and leverage each other’s expertise.”
A comprehensive inventory of system assets, especially industrial embedded devices, becomes even more difficult in light of more porous system boundaries and virtual assets, leading to blind spots as to where and how much risk affects the modern industrial control system. Awareness, education and training of both the OT and IT workforce become the foundation for the effective use of people, process and technology to strengthen industrial control system security.
Achieving these initiatives, however, may be harder than anticipated. Security personnel working to defend their environment focus on the current and immediate threat landscape. For OT and industrial control system, this includes IoT growth, accidental insiders, supply chain issues and malicious external actors. In 2019, the leading business concerns are not fully aligned with the current threat landscape, flagging potential conflict in achieving the desired initiatives if an actual attack against the business occurs.
SANS believes collaboration between the IT and operational technology domains is essential as organisations come to rely more on internal staffing. Data shows that cooperation is improving, but clashes in roles and responsibilities show the potential for conflict. According to survey results, IT takes a leading role in managing corporate security policy and implementing the necessary controls, including into OT’s domain, while OT often controls the budget for safeguarding the industrial control system.
“Internal threats, although accidental, are the second highest overall threat category.”
The goals and objectives of these two domains are not well aligned: IT governance and risk management center on uptime and the protection of information and reputation privacy, while OT focuses on the safety and reliability of cyberphysical processes. To ensure collaboration and reduced risk to the organisation, a common understanding of these key concepts is needed, often requiring a common understanding of terminology, too. The widely known security risk categories of people, process and technology can be viewed as the three pillars for a successful IT and OT convergence strategy.
Effective OT and control system security begins with a clear vision and strategy of where the organisation is and where it wants to go. It depends on the architectural soundness of the entire design and its operations that span OT and IT, and are even external to the enterprise—not just the hardware and software of the system and/or network, but the people and processes as well.
“The activities that can help remediate this concern, remain relatively low as a business concern and, therefore, not a priority despite being a leading initiative.”
“The obvious concern about the risk that people represent—whether they are malicious insiders, careless employees or nation-state bad actors—is consistent across industries,” noted survey co-author and SANS Senior Analyst Barbara Filkins. “We were a little surprised at the lower-ranking concern around process, given that there is significant complexity involved in ICS design, implementation and operation to safeguard OT systems. It is possible recent attacks that almost always include tried-and-true tactics that exploit human-factors might have impacted our respondents’ perceptions.”

Survey co-author and director of SANS Industrials and Infrastructure business portfolio Doug Wylie said, “We know from previous SANS research that the addition of things and mobile devices to ICS represents significant risk. We see in our newest results that practitioners struggle mightily with how to offset these mounting challenges.”
The growing adoption and movement to cloud services, 40% of respondents indicated they use some cloud service represents additional risks with exposure to new threats that need to be comprehended and addressed. Wylie added, “Hyperconnectivity and the rapid introduction of new technology within OT is providing tangible value, but the added complexity that comes with each continues to outpace the readiness of those tasked with safeguarding today’s systems from cyber threats.”




Executive summary
The 2019 SANS OT ICS Cybersecurity Survey explores the challenges involved with design, operation and risk management of an industrial control system ICS, its cyber assets and communication protocols, and supporting operations. This year, SANS focused more broadly on the operational technology, OT domain inside organisations, because industrial control systems are interwoven and interdependent, while also actively exchanging information with a myriad of other systems and processes.
Fundamentally, a modern industrial control system is rarely, if ever, exclusively localised to an isolated, physical control system. Rather, it is an integral part of company operations. Operations now relies on these interactions of industrial control systems with IT, placing new emphasis on the integration of these two domains—especially around communications and data exchange.
Even the lower levels of a modern industrial control system architecture endpoints, field devices, instrumentation, intelligent sensors and actuators now rely on remote connectivity for communication, control, configuration and data collection.
As these boundaries become more fluid, OT and IT teams need other professionals working or active in enterprise IT or operational control systems, such as industrial control system, SCADA, process control, distributed control or building facility automation and control to break down traditional communication barriers to support this new architectural norm for control systems across industries and throughout application domains.
“The greatest challenge is around governance, workforce skills, manpower.”
The 2019 SANS OT ICS Security Survey reveals a growing maturity in identifying potential risk and detecting and remediating actual events. People are considered the leading risk for compromise, signaling the need for a blended approach to addressing OT and industrial control system cybersecurity, one not solely reliant on technology. The top initiatives where respondent organisations are prioritising and committing, budgeting their efforts to increase OT and control system and network security align nicely with the broad risk categories of people, process and technology.
These initiatives emphasize the need to understand and chart the industrial control system environment. Internet connectivity has opened industrial control system network boundaries that historically were closed, well-defined and documented, resulting in the desire and need for visibility into critical communication links—especially wireless extensions to the industrial control system architecture. At the same time, a growing reliance on cloud-based architectures and services reinforces the need for knowing what you have, where information is stored and exchanged, and even where the logic and control functions for the industrial control system reside.
In 2019, the majority of organisations are either adopting or planning to adopt an ongoing strategy or plan that addresses convergence. Based on observations gleaned from the survey, SANS would like to offer advice that organisations should take into account as they shape and implement their convergence strategy.
Perhaps the initial question to be asked is, where should my organisation spend its first dollar on convergence to gain the greatest value? Based on this survey’s results, the answer is simple and definite—people. Knowledgeable people are needed to make qualified decisions around both process and the supporting technology. And, as we have seen, the budget to increase staff understanding, awareness and skills does not necessarily require the largest budget commitment.
“From a technology perspective, moving from away from simplistic blacklisting antivirus to next-generation antivirus solutions, risk measurement and analysis, and comprehensive asset inventories are the biggest challenges for this year.”
Key takeaways
Strategy
- In 2019 business concerns are not aligned with the current threat landscape.
- There is potential conflict in achieving desired initiatives if an actual attack against business occurs.
- Common understanding of these concepts is needed, requiring common understanding of terminology.
- The security risk categories of people, process, technology can be viewed as three pillars for successful IT and OT convergence.
- Effective OT and control system security begins with a clear vision of where the organisation is and where it wants to go.
Execution
- Goals and objectives of the two domains are not well aligned.
- IT governance centers on uptime and protection while OT focuses on safety and reliability.
People
- Collaboration between IT and operational technology domains is essential as organisations come to rely on internal staffing.
- Clashes in roles and responsibilities show the potential for conflict.
- IT takes a leading role in managing corporate security policy while OT controls budget for safeguarding industrial control system.